Published: September 11, 2019 | Updated: March 07, 2024
Cyber security today is a lot like a classic arcade game. No matter how much you pump in the quarters, the space invaders keep coming. Unfortunately, the always imminent “Game Over” carries a more pernicious connotation in reality when losing is not an option.
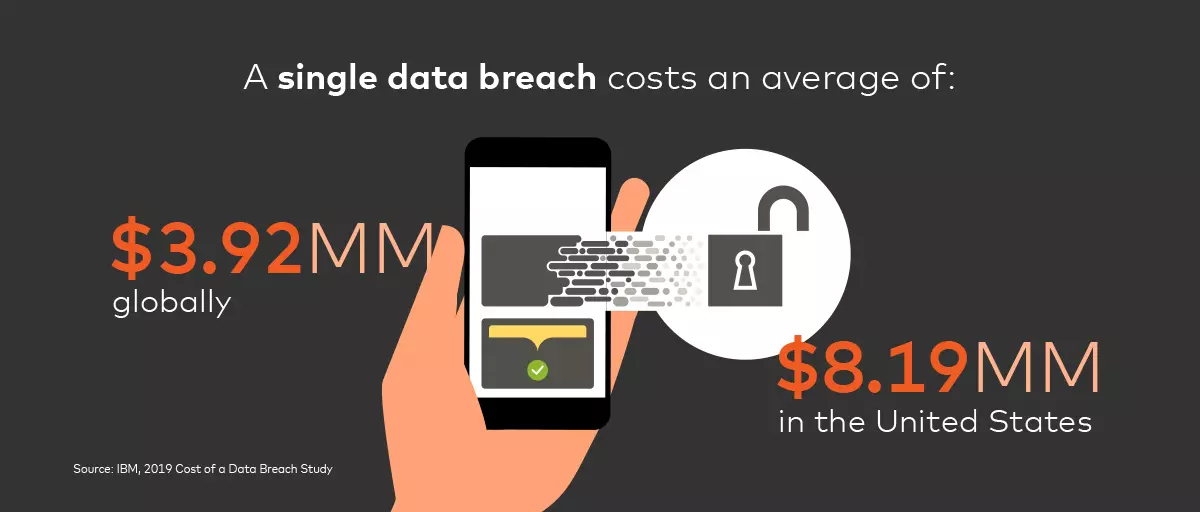
Dramatic year-over-year increases in organizations’ cyber security budgets mean expenses worldwide are predicted to exceed $124 billion in 2019. According to a recent study by IBM, a single data breach costs an average of $3.92 million globally and $8.19 million in the U.S. And that’s not including the costs associated with negative brand perception and increasing regulatory scrutiny. Such ineffective spend on counter measures is exacerbated by inadequate risk estimation on the part of organizations. With data breaches going undetected for an average of 196 days, an invasion can be complete before an organization even mounts a defense.
Data Demands Security
As digital channels proliferate, organizations across all sectors are generating data at exponential rates. These increasing amounts of data affect merchants, financial institutions, facilitated by open banking, and healthcare organizations, due to advances in medical recording, monitoring, and imaging. Organizations are now trying to manage digitization as it expands from the exclusive concern of digital teams to span entire organizations. Yet, conspicuously absent in all this effort is the association of increased digital data with heightened security risks.
At Mastercard, we practice security by design. Our background in global digital payment transactions means we build security into everything we do as standard. Over the years, we have applied our experience in privacy and cyber security to efforts ranging from helping organizations meet the General Data Protection Regulation (GDPR) to assisting with day-to-day security excellence. We are committed to helping protect organizations across the globe.
Context Dictates Action
Traditional cyber security assessments are abstract and qualitative. They function similarly to how antivirus software assigns different kinds of malware to standardized threat levels. Adopting this approach to cyber security fails to frame risks in the context of specific organizational needs and threats. This makes it difficult to understand the impact of investments and effectively allocate resources.
Modern cyber security assessments should be contextual and quantitative. After conducting an initial assessment of the maturity of existing cyber security measures, organizations need to quantify risk by taking into account organization-specific factors such as size, revenue, number of employees, operating region, and industry. Organizations can then calculate the potential impact on different business assets, including personal and financial data, business secrets, intellectual property, and reputation. This process allows organizations to prioritize actions based on impact and improve their risk score over time. Beyond these types of assessments, embedding robust cyber security practices within every level of the organization at the outset of projects makes risk mitigation much easier down the road. This is a key practice at Mastercard and the best way to ensure proactive and robust security systems over time.
In Space Invaders, the alien invasion was ultimately inevitable. The only option was to forestall your impending demise for as long as your quarters held out. But cyber security need not be played by mindlessly plugging coins into a slot. Instead, it should be played by plugging quantitatively evaluated holes with the most effective and efficient solutions. Of course, arcade games often had a hidden code to make players invincible. And the ability to go beyond prioritizing current initiatives to establishing security at the forefront of all future initiatives represents just that.
Please reach out to us to learn more about Mastercard’s cyber security and best-in-class privacy solutions.